Penetration Testing Services
Active security controls for top effectiveness
Demonstrate and improve your organisation’s ability to defend itself against cyber crime.

Overview
Think like an attacker to learn how to efficiently guard your organisation’s high-value corporate assets against external or internal threats. Find out which policies, systems or users are vulnerable to being ambushed and which data or network assets (including those of clients or suppliers) are subsequently endangered at your current security posture. Using quantitative results, CSOs can validate suitable security measures across the value chain, while CIOs can sign-off on calculated security investment priorities and showcase their business value to boards. Let the data help you become battle-ready in the fight against cyber crime.
Benefits
- Understand current security posture strengths and weaknesses;
- Establish a standard baseline for security across the value chain;
- Test the effectiveness of your organisation’s security policies, incident response times and employees’ security awareness;
- Validate and filter specific results of vulnerability scans;
- Validate incident response strategies and strategically improve response times;
- Maintain business system availability;
- Protect your organisation’s (and your clients’) intellectual property.
Download our Penetration Testing Services brochure
We have been dealing with AVeS for a number of years now, and have found them to be one of our best service providers. They are knowledgeable, responsive and thorough in everything they do for us. Nothing is too much trouble, and they attend to our requests promptly.
Popular Services
Targeted Email Phishing Simulation
Test your employees’ ability to identify fraudulent emails, whether they are generic or role-specific, based on the email sender, links, content and request types.- Define the list of email users to be included in the simulated phishing campaign
- Choose email templates based on role, industry or job seniority
- Run simulation on specified email users (1 week)
- Executive findings report
- Report recommendations to the management and executive team
Internal or External Pen Test
Use recent vulnerability assessment findings of the organisation to test the extent security flaws within or into the TCP/IP network on various layers, from network access to applications.- Define the testing parameters
- Choose a test type that balances cost and benefits
- Plan and execute the project based on a best-practice methodology
- Document the results
- Map the findings against the potential risks
- Report recommendations to the management and executive team
Managed Social Engineering Project
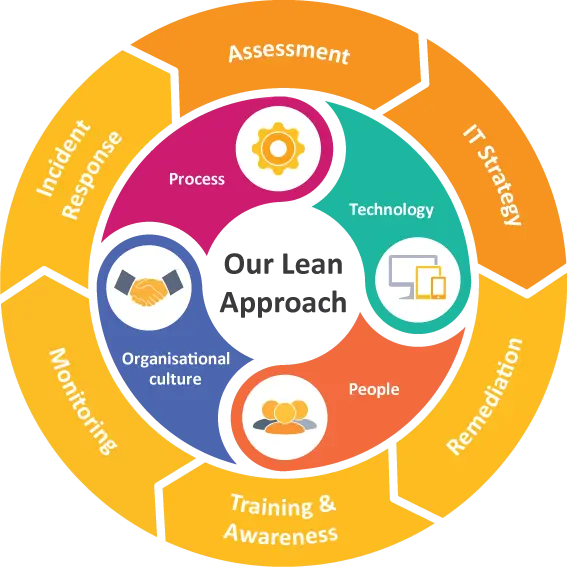
Assess the organisation’s security robustness across people, process and technology to identify its high breach-risk, high business-impact digital assets, and trace easy data exfiltration points from its digital infrastructure.- Define the project parameters
- Choose a test type that balances cost and benefits
- Plan and execute the project based on a best-practice methodology
- Document the results
- Map the findings against the potential risks, enterprise goals, and organisational compliance requirements
- Report recommendations to the management and executive team
Partners

Recommended Service Pairings
Information Security Risk Assessment
Identify where your business risks reside across each of the ISO 27001 requirements and assess how much risk each area poses to your organisation.
Internal or External Vulnerability Assessment
Discover the loopholes in your organisation’s security architecture and how to close them.
Information Security Risk Assessment
Identify where your business risks reside across each of the ISO 27001 requirements and assess how much risk each area poses to your organisation.
Internal or External Vulnerability Assessment
Discover the loopholes in your organisation’s security architecture and how to close them.
Know what you want?
Find what you need to protect your small business or home against cyber criminals.


