Threat & Vulnerability Management Services
Proactive cyber security from the inside-out
Discover the loopholes in your organisation’s security architecture and how to close them.

Overview
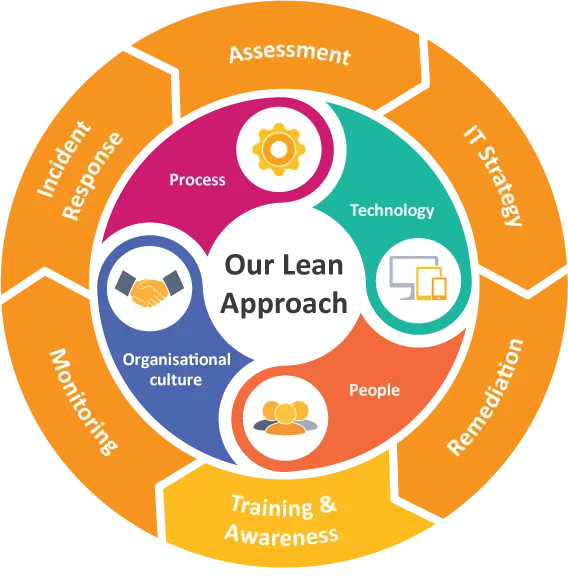
Vulnerability assessments aim to reveal how organisations’ networks, endpoints and web applications could risk providing attackers with unintentional access to confidential company data based on how they have been designed and managed. With a prioritised list of validated security vulnerabilities, our expert team can propose and implement effective countermeasures to proactively address organisations’ unique security challenges before attackers exploit an infrastructure’s ‘weak links’. Improve your IT Security maturity level by becoming proactive and strategic in how you combat data security threats. To validate security vulnerabilities or test the architecture’s resilience against cyber attacks, organisations can pair or follow vulnerability assessments with focused penetration tests.
Benefits
- Pinpoint the most critical operational risks of your IT infrastructure;
- Identify known security vulnerabilities before attackers;
- Evaluate the overall security posture of network systems, endpoint systems, email users and web applications;
- Limit corporate liability;
- Identify the presence of Illegal music, video and other copyrighted material on the corporate network;
- Create or update a detailed network map of the organisation;
- Create an inventory of authorised or unauthorised devices and software on the network.
Download our Threat & Vulnerability Management Services brochure
We have been dealing with AVeS for a number of years now, and have found them to be one of our best service providers. They are knowledgeable, responsive and thorough in everything they do for us. Nothing is too much trouble, and they attend to our requests promptly.
Popular Services
Internal Vulnerability Assessment
Scan your organisation’s internal devices and networks against 50K+ known vulnerabilities.- Scoping meeting:
- 1 to 2-week scan of your network, routers, firewalls, endpoints, servers, ports, software vulnerabilities (not patches), switches, printers.
- Executive assessment report & in-depth action report
- Board or management presentation of assessment findings
External Vulnerability Assessment
Scan your organisation’s externally-facing devices and networks against 50K+ known vulnerabilities.- Scan of your websites, external-facing firewalls, web apps, internet-connected servers, public IPs
- Executive assessment report & in-depth action report
- Board or management presentation of assessment findings
Monthly VA-as-a-service Subscription
Monthly internal vulnerability assessments with a dedicated, virtual vulnerability scanner that scans your organisation’s internal devices and networks against 50K+ known vulnerabilities.- Daily vulnerability scan of new devices on the network
- Weekly scan of all the devices and networks
- Monthly executive assessment report & in-depth action report
- Near real-time alerts to IT security staff of critical device or network vulnerabilities
Recommended Service Pairings
Penetration Testing Services
Test the effectiveness of your people, process and technology’s ability to defend the organisation against cyber crime.
Information Security Risk Assessment
Identify where your business risks reside across each of the ISO 27001 requirements and assess how much risk each area poses to your organisation.
Penetration Testing Services
Test the effectiveness of your people, process and technology’s ability to defend the organisation against cyber crime.
Information Security Risk Assessment
Identify where your business risks reside across each of the ISO 27001 requirements and assess how much risk each area poses to your organisation.
Know what you want?
Find what you need to protect your small business or home against cyber criminals.


